The Shodan blog posted some trends in internet exposure, which like most of the Shodan research is very interesting.
One part that caught my eye was this.
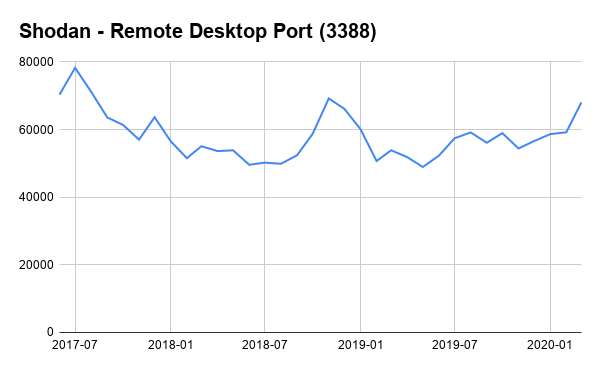
The number of devices exposing RDP to the Internet has grown over the past month which makes sense given how many organizations are moving to remote work. It’s surprising how the number of RDP instances actually went up after the initial Microsoft bulletin on Bluekeep in May 2019. And then it dropped sharply in August once a series of issues were revealed (DejaBlue) that impacted newer versions of RDP. A common tactic we’ve seen in the past by IT departments is to put an insecure service on a non-standard port (aka security by obscurity). To that point, this is how the exposure for RDP looks like on an alternate port (3388) that we’ve seen organizations use:
Trends in Internet Exposure
Now, I find this very interesting, and somewhat concerning. Of course, tech teams are stretched very thin during this time. We’re in an unprecedented time where many organisations have had to adopt remote working very quickly.
While there has been a lot of attention diverted towards Zoom, that is only the tip of the iceberg. The use of insecure tools or protocols isn’t the issue – it’s merely a manifestation which highlights the point that organisations are trying to enable whatever they can to keep the workforce productive.
Speaking with numerous friends, peers, and ex-colleagues, many have spoken about the relaxing of security controls in order to make remote working easier. One company going as far as turning off 2FA so that employees could log in quicker, and so that the IT team didn’t have to deal with unnecessary support tickets.
I don’t fault these organisations at all – these are tough times we’re in, and many are worried that should social distancing go on for an extended period there may not be an organisation to come back to.
On the flip side, this is an awful lot of technical security debt to accrue. In a few months, once the world starts spinning again, and we’re back to polluting it at the usual rate, the security that has been undone, won’t be so easy to fix. Instead, we’ll probably see for years to come the repercussions of decisions made today.
It will be akin to finding a firewall with the any-any rule at the top, added no doubt by some well-intentioned admin in a desperate attempt to fix a production issue at 3am some 2 years prior. And by that time neither that admin is employed, and no-one in the business wants to take the responsibility of removing the rule. So it gets documented, accepted as a risk, and lives on as a legacy system.
While that may be a bit of an extreme example and totally not based on any real life experience. I would implore any organisations relaxing security to support their organisations in this time to document all decisions, even if it amounts to only writing down two lines on a text document. That way, once things are back to normal and everyone has breathing space, you’ll be somewhat better placed to unpack all the decisions and pay off some of that technical debt.
